In 2025, decentralized finance (DeFi) protocols faced a renewed wave of multi-million dollar exploits, with oracle price feed vulnerabilities at the epicenter. The sophistication of these attacks has outpaced many security measures, resulting in high-profile losses and exposing systemic risks in DeFi lending markets. As protocols scale and new assets are integrated, the reliance on accurate, tamper-resistant price feeds is more critical than ever.
Why Oracles Are the Achilles’ Heel of DeFi Lending
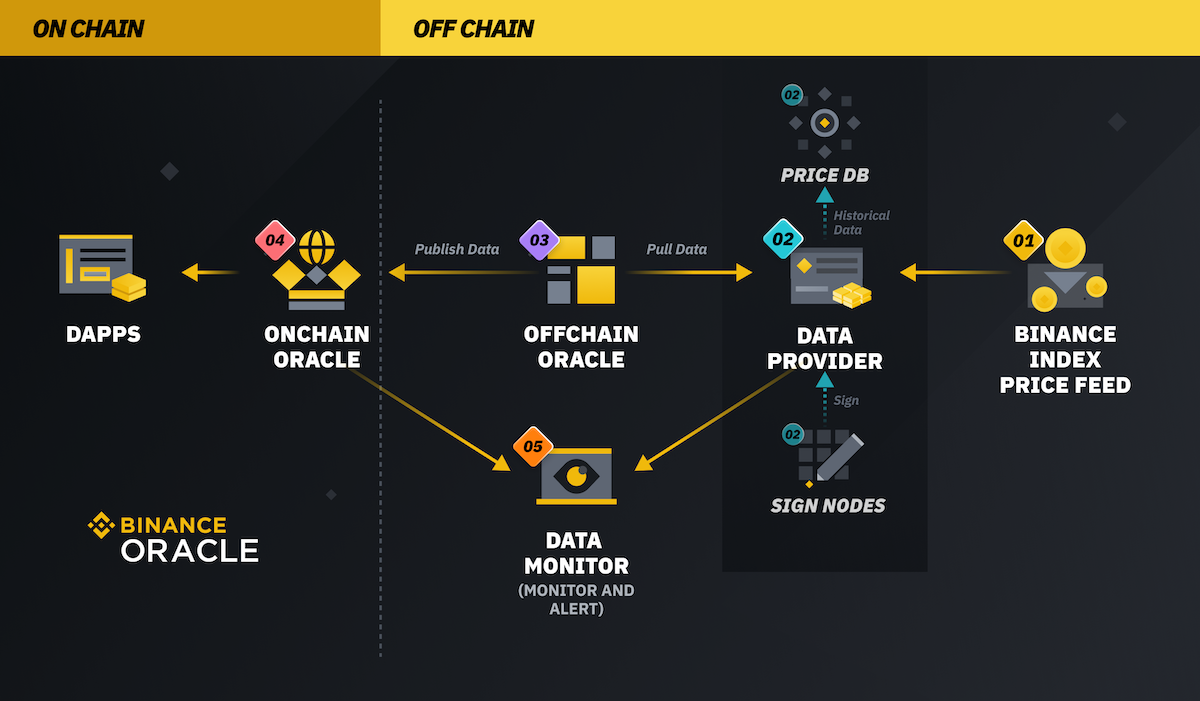
Oracles act as bridges between blockchains and external data sources. In DeFi lending, they provide real-time asset prices that determine collateral values and borrowing limits. However, when oracles malfunction or are manipulated, attackers can exploit these flaws to drain protocol liquidity.
The Moonwell exploit on November 4,2025, is emblematic. A bug in a Chainlink-supplied rsETH/ETH price feed mispriced a tiny deposit, 0.02 wrstETH, as $5.8 million. This allowed an attacker to borrow over 20 wstETH repeatedly, extracting approximately 292 ETH (worth over $1 million at the time) from Moonwell’s Base network deployment. It was Moonwell’s fourth major hack in three years, a stark reminder that even established protocols remain vulnerable.
Recent Exploits: Anatomy of Oracle Manipulation Attacks
The Moonwell incident was not isolated. In May 2025, Demex’s Nitron platform lost nearly $950,559 after an attacker manipulated a deprecated dGLP vault’s oracle value by donating fsGLP to artificially inflate its redemption rate. The compromised data propagated across Nitron markets via the Demex oracle; using this fake collateral value, the attacker borrowed real assets and exited with the loot.
June brought an even larger exploit: Resupply Lending Protocol suffered a $9.6 million loss when a newly deployed crcrvUSD vault with low liquidity was targeted for price manipulation. The attacker forced the exchange rate within ResupplyPair to zero, minting massive reUSD loans for negligible collateral and directly impacting wstUSR markets.
Common threads run through these attacks:
- Poorly secured or single-source oracles
- Lack of safeguards against sudden price anomalies
- Failure to deprecate or cap risk on legacy vaults
This pattern echoes earlier attacks like Mango Markets (October 2022), where flash loans were used to manipulate token prices and extract $110 million, demonstrating that lessons from past exploits are still being painfully relearned.
The Mechanics Behind Flash Loan Oracle Attacks
Flash loans remain a preferred tool for attackers targeting vulnerable price feeds. These uncollateralized loans allow hackers to borrow vast sums instantaneously, enough to move thinly traded markets or manipulate DEX prices observed by protocol oracles.
The typical attack sequence:
- An attacker takes out a flash loan in one or more assets.
- This capital is used to inflate (or deflate) token prices on low-liquidity pools monitored by protocol oracles.
- The manipulated price is recorded by the protocol’s smart contract as genuine market value.
- The attacker uses this false price as collateral to borrow real assets, or triggers liquidations against other users, before repaying their flash loan within the same transaction block.
This cycle can be executed in seconds with no initial capital at risk for the attacker, making robust oracle design essential for any DeFi lending platform seeking long-term viability and user trust.
Mitigation: From Multi-Feed Oracles to Smart Contract Insurance
The industry response has focused on several fronts:
- Oracle redundancy: Using multiple independent data sources to cross-verify prices reduces single points of failure (learn more here).
- Anomaly detection: Implementing validation logic that automatically rejects suspicious price spikes or drops before they impact protocol state.
- Aggressive deprecation policies: Disabling legacy vaults promptly and capping risk exposure when migrating users away from outdated contracts.
- Smart contract insurance: Coverage products now specifically address oracle manipulation risks, offering protection against losses from faulty feeds and incentivizing best practices in protocol design.
Despite these improvements, the rapid pace of DeFi innovation means new oracle price feed vulnerabilities continue to emerge. Attackers are increasingly targeting edge cases, such as low-liquidity vaults or deprecated collateral types, where protocol teams may have deprioritized monitoring. The Resupply Lending Protocol exploit demonstrated how a single overlooked parameter can cascade into a multi-million dollar loss, even for protocols with otherwise robust security postures.
Insurance providers and protocol designers are responding by integrating real-time monitoring and automated circuit breakers. These systems can pause borrowing or liquidations when abnormal oracle data is detected, buying time for human intervention before catastrophic losses occur. In parallel, third-party insurance markets are evolving: smart contract insurance products now routinely cover losses from oracle failures and manipulation, with premiums adjusted dynamically based on observed risk factors.
The Strategic Case for Multi-Layered Oracle Protection
The events of 2025 have made it clear that oracle risk mitigation must be multi-layered. Relying solely on the reputation of a single oracle provider is no longer defensible. Leading protocols are now:
- Combining on-chain and off-chain oracles to diversify data sources
- Incentivizing white-hat hackers through bug bounty programs focused on price feed logic
- Deploying failover mechanisms that default to conservative pricing if anomalies are detected
- Engaging in ongoing audits and real-time threat intelligence sharing across the DeFi ecosystem
This layered approach not only reduces the attack surface but also signals to users and institutional partners that security remains paramount. For investors evaluating DeFi lending platforms, due diligence should now include direct questions about oracle architecture, anomaly detection routines, and the scope of any active insurance policies.
Looking Ahead: Building Trust in DeFi Lending Markets
The scale of losses from recent exploits provides $1 million at Moonwell, $950,559 at Nitron Demex, $9.6 million at Resupply, underscores the financial stakes involved. As more capital flows into decentralized lending markets, user trust hinges on demonstrable improvements in protocol security.
A technical analysis of the Moonwell hack illustrates how quickly vulnerabilities can be exploited when price feeds fail. The takeaway for founders and users alike: robust oracles are not optional infrastructure, they are existential to protocol survival.
For those seeking actionable guidance on evaluating oracles and mitigating risk exposure across portfolios, resources like DepegWatch’s deep dive into real-world exploits provide essential context for navigating an increasingly complex landscape.





No comments yet. Be the first to share your thoughts!