
On March 17,2026, block 30488585 on Polygon zkEVM lit up security alerts when KeomProtocol, a dormant Compound-fork lending protocol, lost $94K to a crafty attacker. The culprit? A logic flaw in KToken’s redeemFresh() function that let the exploiter bypass balance checks and siphon cTokens unchecked. With the protocol’s Twitter silent for a year, this KeomProtocol exploit serves as a stark reminder: even established codebases harbor redeemFresh vulnerability risks, demanding layered defenses like DeFi lending insurance.
This incident echoes past lending mishaps, where subtle math errors opened floodgates to theft. Attackers thrive on overlooked caps and misordered calculations, turning trusted redemption logic into a liability. For DeFi users and developers, the lesson cuts deep: smart contract exploit coverage isn’t optional; it’s the strategic hedge against code’s hidden fractures.
Cracking the redeemFresh Logic Flaw
KeomProtocol’s KToken contract, mimicking Compound’s structure, intended redeemFresh() to handle token redemptions efficiently by accruing interest and applying exchange rates. But lines 992-993 introduced a fatal misstep. After calculating redeemTokens via exchange rate multipliers, the function erroneously capped them against the user’s cToken balance post-accrual, not pre. This sequencing glitch allowed an attacker with manipulated positions to redeem far more underlying assets than their actual holdings warranted.
Strategic insight: Logic bugs like this evade pattern-based audits, which flag reentrancy or overflows but miss operation order. Protocols forking Compound must rigorously diff their variants; KeomProtocol’s inactivity amplified the oversight. Developers, prioritize fuzzing redemption paths and formal verification for cToken drain protection.
Attack Vector: From Setup to $94K Drain
The assault unfolded methodically. First, the attacker supplied minimal collateral to mint cTokens, then triggered accrual manipulations via flash loans on Polygon zkEVM’s chain ID 1101. Calling redeemFresh() exploited the cap flaw: redeemTokens computed generously from inflated rates, then clipped to a balance that hadn’t deducted prior redemptions fully. Result? Iterative drains netting $94K in underlying tokens, swapped out swiftly.
Compare this to Yearn Finance’s yETH pool, where a numerical bug minted infinite LP tokens for $9M loss. Both reveal lending’s Achilles heel: redemption math under stress. KeomProtocol’s Polygon zkEVM hack proves small protocols aren’t immune; low TVL invites low-effort hits.
Strategic Imperative: Bolstering DeFi Lending Insurance
Exploits like this erode trust, but DeFi lending insurance rebuilds it. Platforms now integrate coverage akin to Algem’s InsureDAO partnership, shielding staked assets from smart contract exploit coverage gaps. For institutions, bundle cToken positions with parametric policies triggering on oracle-confirmed drains. Retail? Opt for diversified pools covering forks like Keom’s.
Owen’s take: Diversification reigns, but insurance amplifies it. Post-exploit, scan your exposures; if Polygon zkEVM lending dominates, layer cToken drain protection now. Protocols, embed insurance hooks pre-launch; users, demand them. This $94K wake-up call charts the path forward.
Institutions eyeing Polygon zkEVM exposure should prioritize protocols with proven audit trails and active governance. Yet audits alone falter against logic quirks like this redeemFresh vulnerability; that’s where smart contract exploit coverage steps in as the backstop. Pair it with on-chain monitoring tools to detect accrual anomalies early, turning potential $94K hits into contained incidents.
Layered Defenses: Beyond Code Fixes
KeomProtocol’s silence post-exploit spotlights a broader issue: dormant projects breed complacency. Active protocols counter this with bug bounties, continuous integration testing, and oracle redundancies. But for users, the real shield lies in diversified insurance stacks. Consider parametric triggers that auto-payout on confirmed drains, bypassing slow claims processes. This Polygon zkEVM hack validates such mechanisms, as seen in rising adoption among lending forks.
Key DeFi Lending Safeguards
-

Diversify protocols: Spread assets across Aave, Compound, and Morpho to avoid single-protocol exploits.
-
Integrate insurance: Use Nexus Mutual or InsureDAO for smart contract coverage against bugs like redeemFresh.
-
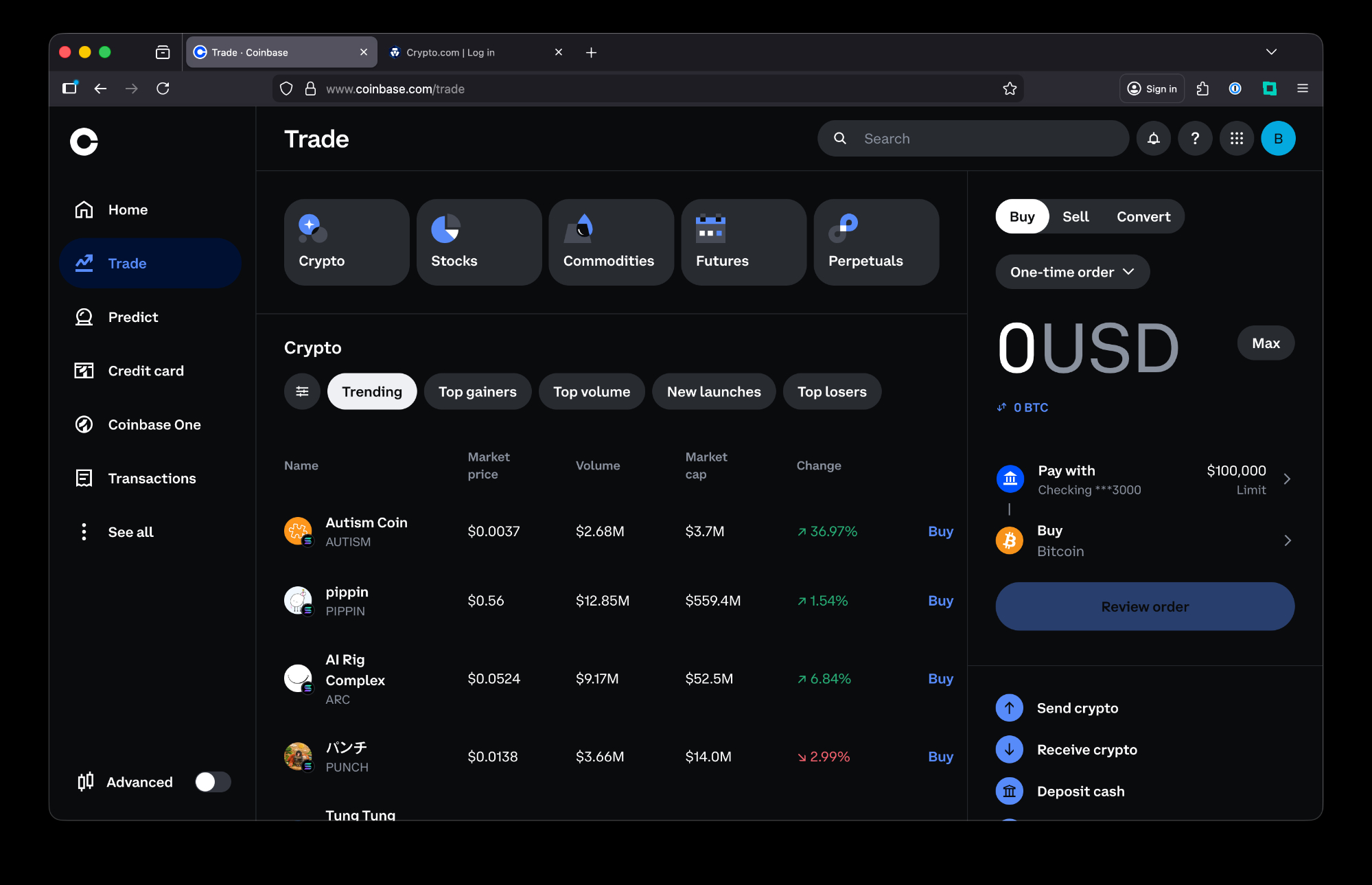
Monitor positions with DeFi Saver and Zapper.fi for real-time health checks and alerts.
-
Prioritize audited protocols: Verify PeckShield or Certik audits before depositing.
-

Use hardware wallets: Secure funds via Ledger or Trezor for lending interactions.
Developers forking Compound must evolve: implement pre/post-accrual balance invariants in redemption logic. Fuzzers exposed Keom’s flaw retrospectively; make them standard. Users, audit your cToken positions quarterly, favoring protocols with cToken drain protection riders. The $94K loss, while modest, signals escalating scrutiny on zkEVM chains where gas efficiency tempts shortcuts.
Owen’s Portfolio Playbook: Insurance-Integrated Lending
With 18 years steering multi-asset risks, I’ve seen insurance evolve from afterthought to core allocation. In DeFi, integrate it via yield-bearing wrappers that embed coverage, optimizing APY net of premiums. For DeFi lending insurance, target providers excelling in lending-specific perils: logic errors, oracle fails, and governance attacks. Diversify across chains; zkEVM’s speed amplifies bugs, so balance with Ethereum mainnet stalwarts.
Post-Keom, zkEVM TVL may dip, but resilient protocols rebound faster under insured auspices. Scan dashboards for KeomProtocol exploit echoes; if redemption volumes spike oddly, exit swiftly. My principle holds: diversification via insurance fortifies the front line, ensuring one flaw doesn’t unravel the position. Protocols heeding this build moats; users wielding it, empires.
Lending’s future hinges on this fusion: ironclad code wedded to financial safeguards. As zkEVM matures, expect tighter forks and richer coverage menus. Position accordingly, and exploits become footnotes, not fractures.





